Imagine waking up one morning to find your entire cryptocurrency portfolio wiped out not because of a market crash, but because your wallet was not properly encrypted. This nightmare is real for thousands of crypto holders every year.
The problem is simple: most people buy Bitcoin or other cryptocurrencies without truly understanding wallet encryption and bitcoin security. They store their crypto wallet keys carelessly, skip basic encryption steps, and leave their digital assets wide open to hackers.
The good news? Proper wallet encryption is not complicated. In this comprehensive guide, you will learn everything about crypto currency wallet security from understanding how crypto wallet keys work to implementing advanced bitcoin security practices. Whether you are a beginner or an experienced investor, this guide will help you secure your digital assets like a professional.
Section 1: What Is Wallet Encryption? A Complete Overview
1.1 Understanding Wallet Encryption Basics
Wallet encryption is the process of securing your cryptocurrency wallet using cryptographic algorithms that make your private keys and sensitive data unreadable to unauthorized users. When you encrypt your crypto wallet, you are essentially putting your digital assets behind a mathematical lock that only you can open.
At its core, wallet encryption converts your readable wallet data into an encrypted format using complex algorithms like AES-256 (Advanced Encryption Standard). This means even if a hacker gains access to your wallet file, they cannot read or use your private keys without the correct decryption password.
Key Components of Wallet Encryption:
- Private Key: A unique 256-bit number that proves ownership of your cryptocurrency
- Public Key: Derived from your private key, used to receive funds
- Seed Phrase: A human-readable backup of your private key (usually 12-24 words)
- Encryption Password: The password that locks and unlocks your encrypted wallet
- Wallet File: The encrypted file stored on your device
1.2 Why Wallet Encryption Is Critical for Bitcoin Security
Bitcoin security depends entirely on the protection of your private keys. Unlike traditional banks where a customer service team can recover your account, cryptocurrency transactions are irreversible. Lose your private key without proper wallet encryption, and your funds are gone forever.
According to blockchain analytics, billions of dollars worth of cryptocurrency have been lost or stolen due to poor wallet encryption and weak bitcoin security practices. The decentralized nature of cryptocurrency means there is no central authority to restore lost funds — which makes cryptocurrency wallet security your personal responsibility.
Real-Life Example:
In 2021, a crypto investor lost over $2 million worth of Bitcoin because they stored their crypto wallet key in an unencrypted text file on their desktop. A malware attack scanned their computer, found the file, and transferred all funds within minutes. Proper wallet encryption would have prevented this entirely.
1.3 Types of Wallet Encryption Methods
Understanding different encryption methods helps you choose the right cryptocurrency wallet security approach for your needs:
AES-256 Encryption
AES-256 is the gold standard for wallet encryption. Used by governments, banks, and top cryptocurrency wallets, this encryption method would take billions of years to crack with current computing power. Most reputable software wallets use AES-256 to protect your crypto wallet keys.
Hierarchical Deterministic (HD) Wallet Encryption
HD wallets generate all crypto wallet keys from a single seed phrase. This means you only need to back up one seed phrase to recover all your wallet’s private keys. Bitcoin security is enhanced because you can generate new addresses for each transaction without creating new backups.
Multi-Signature Encryption
Multi-signature (multisig) wallet encryption requires multiple private keys to authorize a transaction. For example, a 2-of-3 multisig setup means 2 out of 3 designated private keys must sign any transaction. This is one of the strongest bitcoin security measures for high-value holdings.
1.4 Hot Wallets vs Cold Storage: Encryption Comparison
| Feature | Hot Wallet | Cold Storage |
| Internet Connection | Always online | Offline (air-gapped) |
| Encryption Type | Software AES-256 | Hardware + Software |
| Bitcoin Security Level | Medium | Very High |
| Convenience | High (instant access) | Low (manual process) |
| Best For | Daily transactions | Long-term storage |
| Example | Trust Wallet, MetaMask | Ledger Nano X, Trezor |

Section 2: Crypto Wallet Keys — How They Work & How to Protect Them
2.1 What Are Crypto Wallet Keys?
Crypto wallet keys are the foundation of all cryptocurrency ownership. Unlike physical keys, crypto wallet keys are mathematical values generated by complex cryptographic algorithms. There are two types: public keys and private keys, and understanding both is essential for strong wallet encryption.
Your private key is like the master password to your cryptocurrency it proves you own the funds associated with a wallet address. Your public key (and the wallet address derived from it) is like your bank account number you can share it freely to receive funds.
The Crypto Wallet Key Generation Process:
- Step 1: A random 256-bit number is generated as your private key
- Step 2: The private key is run through the Elliptic Curve Digital Signature Algorithm (ECDSA)
- Step 3: This produces your public key
- Step 4: The public key is hashed twice (SHA-256 then RIPEMD-160) to create your wallet address
- Step 5: All of this is secured by your wallet encryption password
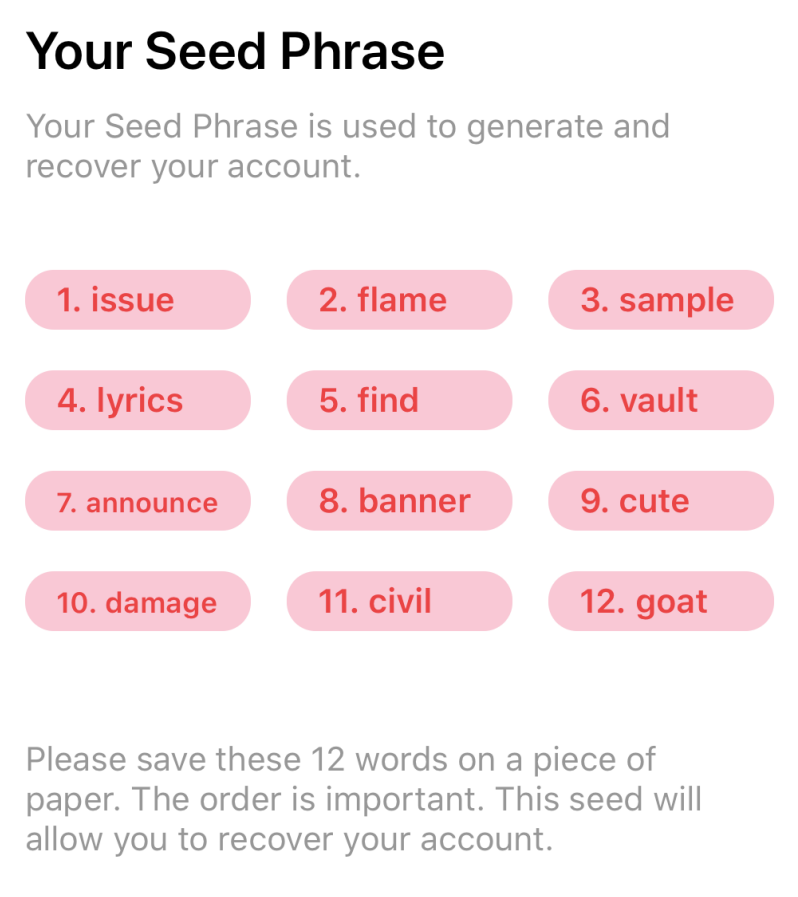
2.2 Seed Phrase Security: The Backbone of Cryptocurrency Wallet Security
A seed phrase (also called a recovery phrase or mnemonic phrase) is a human-readable representation of your crypto wallet keys. Typically consisting of 12 to 24 words from the BIP39 wordlist, your seed phrase can regenerate all your private keys if your wallet is lost or damaged.
This is both the greatest strength and greatest vulnerability of modern cryptocurrency wallet security. Anyone who knows your seed phrase has complete access to all your cryptocurrency forever, with no way to revoke access.
Seed Phrase Security Best Practices:
- Never store your seed phrase digitally — no photos, no cloud storage, no email
- Write it on paper and store in multiple secure physical locations
- Consider using a metal seed phrase backup for fire and water resistance
- Never share your seed phrase with anyone — legitimate services never ask for it
- Test your seed phrase backup before depositing large amounts
2.3 Private Key Protection Strategies
Private key protection is the most critical aspect of bitcoin security. Your private key is the only proof of ownership in the cryptocurrency world — lose it, and your funds are unrecoverable. Share it, and your funds are immediately at risk.
Hardware Security Modules (HSM)
For institutional bitcoin security, Hardware Security Modules provide the highest level of private key protection. HSMs are tamper-proof devices designed specifically to generate, store, and manage crypto wallet keys. They are used by cryptocurrency exchanges and institutional investors managing large amounts.
Paper Wallets
A paper wallet involves generating your crypto wallet keys offline and printing them on paper. When done correctly with proper wallet encryption protocols, paper wallets can be extremely secure. However, they require careful handling and are vulnerable to physical damage.
Encrypted USB Storage
Storing an encrypted backup of your crypto wallet keys on an encrypted USB drive provides a good balance of security and accessibility. Use AES-256 encryption for the USB drive and keep it in a secure physical location.
2.4 Common Crypto Wallet Key Mistakes to Avoid
- Storing private keys in plain text files on internet-connected devices
- Taking screenshots of seed phrases on smartphones (synced to cloud)
- Using weak passwords for wallet encryption
- Keeping all crypto wallet keys in a single location
- Sharing private keys or seed phrases with anyone online
- Using unverified wallet software that may contain malware
Section 3: Bitcoin Security Advanced Strategies for 2024
3.1 Why Bitcoin Security Requires a Multi-Layer Approach
Bitcoin security is not a single action but a layered system of protections. Just as a bank vault uses multiple security measures — cameras, guards, thick walls, time locks — effective bitcoin security combines wallet encryption, hardware security, network security, and behavioral practices.
The 2024 crypto landscape has seen increasingly sophisticated attacks targeting individuals and institutions. Phishing attacks, SIM swapping, clipboard hijacking malware, and social engineering have all been used to steal crypto wallet keys. A multi-layer bitcoin security approach addresses all these attack vectors.
3.2 Two-Factor Authentication (2FA) for Enhanced Bitcoin Security
Two-factor authentication adds a critical second layer to your bitcoin security. Even if an attacker somehow obtains your wallet password, 2FA prevents them from accessing your funds without the second verification factor.
2FA Methods Ranked by Security:
- Hardware Security Keys (YubiKey) — Most Secure
- Authenticator Apps (Google Authenticator, Authy) — Very Secure
- Email-based 2FA — Moderate Security
- SMS-based 2FA — Least Secure (vulnerable to SIM swapping)
3.3 Cold Storage: The Gold Standard of Bitcoin Security
Cold storage refers to keeping your crypto wallet keys completely offline, away from any internet connection. This is the most secure method for long-term bitcoin security, used by major exchanges to protect the majority of customer funds.
Cold storage eliminates the primary attack vector for cryptocurrency theft — internet-based attacks. A hacker cannot remotely steal crypto wallet keys that have never touched the internet.
Cold Storage Options:
- Hardware Wallets (Ledger Nano X, Trezor Model T) — Most popular cold storage
- Air-Gapped Computers — Dedicated offline computers for signing transactions
- Paper Wallets — Physical printed crypto wallet keys
- Metal Backup Devices — For seed phrase storage resistant to fire and water
3.4 Network Security for Cryptocurrency Wallet Security
Even the best wallet encryption can be undermined by poor network security. Many bitcoin security breaches happen not because of weak encryption but because of compromised network connections or devices.
Network Security Best Practices:
- Never access your cryptocurrency wallet on public WiFi without a VPN
- Use a dedicated device for cryptocurrency transactions
- Keep your operating system and wallet software updated
- Use a reputable antivirus and anti-malware solution
- Enable firewall protection on all devices used for crypto
- Verify website URLs carefully before entering wallet credentials (phishing prevention)
Section 4: Cryptocurrency Wallet Security Step-by-Step Implementation Guide
4.1 Setting Up Wallet Encryption: A Beginner’s Step-by-Step Guide
Implementing wallet encryption does not have to be complicated. Follow this step-by-step guide to secure your cryptocurrency wallet from the ground up:
Step 1: Choose the Right Wallet
Select a wallet appropriate for your needs. For beginners, a reputable software wallet with built-in wallet encryption (like Trust Wallet or Exodus) is a good start. For larger amounts, immediately consider a hardware wallet.
Step 2: Create a Strong Encryption Password
Your wallet encryption password is your first line of defense. Create a password that is: at least 16 characters long, contains uppercase and lowercase letters, includes numbers and special characters, and is completely unique (not used for any other service).
Step 3: Secure Your Seed Phrase
When your wallet generates your seed phrase, write it down immediately on paper. Do not type it, photograph it, or store it digitally. Store this paper in a secure location — a fireproof safe is ideal.
Step 4: Enable All Available Security Features
Enable two-factor authentication, biometric authentication (if available), and any additional PIN or password requirements your wallet offers. The more layers of bitcoin security, the better.
Step 5: Test Your Backup
Before depositing significant funds, test that your seed phrase works by restoring your wallet on a separate device. This confirms your backup is correct and your cryptocurrency wallet security is properly set up.
4.2 Cryptocurrency Wallet Security Audit Checklist
- Wallet encryption is enabled with a strong, unique password
- Seed phrase is written on paper and stored securely offline
- Two-factor authentication is enabled on all related accounts
- Wallet software is up to date
- No seed phrase or private key stored digitally
- Hardware wallet used for holdings above $1,000
- Regular security audits conducted
- Network security measures in place
- Emergency recovery plan documented
- Family or trusted person knows how to access funds in emergency
4.3 Recovering a Cryptocurrency Wallet Bitcoin Security During Recovery
Even the best bitcoin security plan needs an emergency recovery procedure. Knowing how to recover your wallet safely is as important as securing it in the first place.
Safe Recovery Steps:
- Use a trusted, clean device that has never been compromised
- Download wallet software only from the official website
- Verify the software checksum before installation
- Enter your seed phrase only on the wallet software interface never on websites
- Re-enable all wallet encryption and security features after recovery
- Transfer funds to a new wallet address immediately if you suspect the seed phrase was compromised
4.4 Advanced Wallet Encryption for High-Value Holdings
If you are managing cryptocurrency holdings above $10,000, basic wallet encryption is not enough. Implement these advanced bitcoin security measures:
Geographic Distribution
Store seed phrase backups in multiple geographic locations. A fire, flood, or theft at one location should not result in permanent loss of access to your cryptocurrency.
Shamir’s Secret Sharing
This cryptographic technique splits your seed phrase into multiple shares, requiring a minimum number of shares to reconstruct the original. For example, split into 5 shares where any 3 can reconstruct the seed phrase — ideal for families or business partnerships.
Multi-Signature Wallet Setup
Set up a multi-signature wallet requiring 2-of-3 or 3-of-5 signatures for any transaction. This prevents single points of failure in your bitcoin security setup and is highly recommended for business cryptocurrency management.
Section 5: Frequently Asked Questions About Wallet Encryption & Bitcoin Security
Q1: What is the safest type of wallet encryption?
AES-256 encryption combined with hardware wallet storage is currently the safest form of wallet encryption. Hardware wallets like the Ledger Nano X use secure element chips specifically designed to protect crypto wallet keys, making them resistant to both physical and remote attacks.
Q2: Can wallet encryption be hacked?
Properly implemented AES-256 wallet encryption cannot be practically brute-forced with current technology. However, bitcoin security breaches usually happen through phishing attacks, malware, social engineering, or poor operational security — not by breaking the encryption algorithm itself. This is why comprehensive cryptocurrency wallet security involves much more than just enabling encryption.
Q3: What happens if I forget my wallet encryption password?
If you forget your wallet encryption password, you can restore your wallet using your seed phrase. This is why seed phrase security is so critical — your seed phrase is the ultimate backup for all your crypto wallet keys. Without either your password or seed phrase, access to your funds is permanently lost.
Q4: How often should I update my wallet encryption?
You should update your wallet encryption password if you suspect it has been compromised, if someone has had physical access to your device, or at least annually as a general bitcoin security practice. Always ensure your wallet software is updated to the latest version to benefit from security patches.
Q5: Is cryptocurrency wallet security the same for all coins?
The fundamental principles of wallet encryption and bitcoin security apply across most cryptocurrencies. However, some coins have specific wallet security considerations. Bitcoin uses ECDSA for key generation, while Ethereum uses similar but distinct standards. Multi-coin wallets like Trust Wallet handle these differences automatically.
Q6: What is the difference between a hot wallet and cold storage for bitcoin security?
Hot wallets are connected to the internet and offer convenient access but face more security risks. Cold storage keeps your crypto wallet keys completely offline, making them immune to remote attacks but less convenient for regular transactions. The best bitcoin security strategy uses both: cold storage for long-term holdings and hot wallets for spending money.
Q7: Should I use a hardware wallet for wallet encryption?
Yes, hardware wallets provide the best wallet encryption for most users. They store your crypto wallet keys in a secure chip that never exposes the private key to your computer or the internet. For any amount of cryptocurrency you cannot afford to lose, a hardware wallet is strongly recommended for optimal cryptocurrency wallet security.
Conclusion: Take Control of Your Bitcoin Security Today
Wallet encryption is not optional in today’s cryptocurrency landscape — it is essential. Your crypto wallet keys represent real financial value, and without proper wallet encryption and bitcoin security practices, that value is at serious risk.
Throughout this guide, you have learned what wallet encryption is and how it works, how crypto wallet keys are generated and protected, advanced bitcoin security strategies for 2024, step-by-step cryptocurrency wallet security implementation, and how to recover safely while maintaining bitcoin security.
The path to strong cryptocurrency wallet security starts with a single step. Whether you implement basic wallet encryption today or upgrade to a full hardware wallet cold storage setup, every improvement you make significantly reduces your risk. Do not wait for a security breach to take action. Implement these wallet encryption and bitcoin security practices today, and protect your digital assets with the same care you would protect your most valuable physical possessions.
🔐 Take Action Now: Audit your current wallet encryption setup, secure your seed phrase, and consider upgrading to a hardware wallet for maximum bitcoin security!



Pingback: What Is a Hardware Wallet? 5 Reasons Your Crypto Isn't Safe Without One - Investova
Pingback: Adrian CryptoProNetwork: The Complete 2026 Guide for Crypto Investors - Investova
Why an Exit Plan is Essential:
During a bull run, greed takes over — and most people forget to sell at the top
Locking in profits is just as important as investing in the first place
Set your targets in advance — for example, “I’ll sell X when I’m up 50%”